
Author
Harley Sugarman
Published on
In September 2023, attackers took down MGM Resorts. Slot machines went offline, hotel room keys stopped working, ATMs went dark, and around $100 million evaporated from their market cap in a single quarter.
The attackers didn’t send a phishing email.
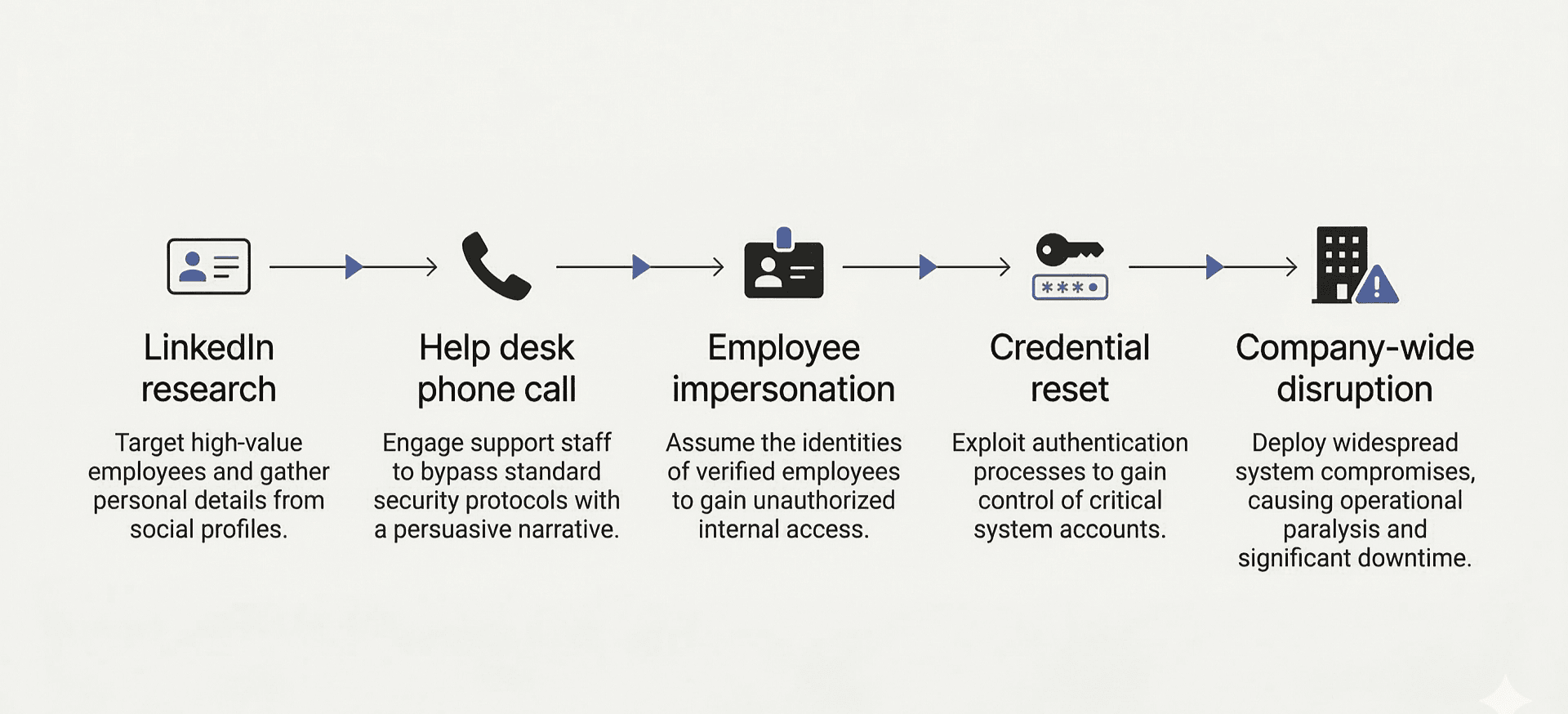
They pulled information from LinkedIn, called the IT help desk, spent about ten minutes impersonating an employee, and walked out with login credentials. The help desk employee who took that call had sat through the same security training as everyone else. It gave them zero preparation for what happened next.
Most security awareness programs are still training employees to spot a badly formatted email.
How the category got stuck
The security awareness training market was built around one threat: mass phishing simulations. KnowBe4 turned that into a billion-dollar business. Proofpoint built it into their enterprise stack. The playbook was simple - run mock phishing campaigns, track who clicks, send training to the clickers, report the improvement to the board.
It worked, to a point. Click rates went down. Compliance boxes got checked. The whole industry optimized harder for the thing it was already measuring.
But click rates on simulated phishing emails were always the wrong thing to measure. Employees figured out how to game it. And attackers noticed that companies were training people to spot suspicious emails, so they stopped sending suspicious emails.
They made phone calls instead.
Three things broke the old model
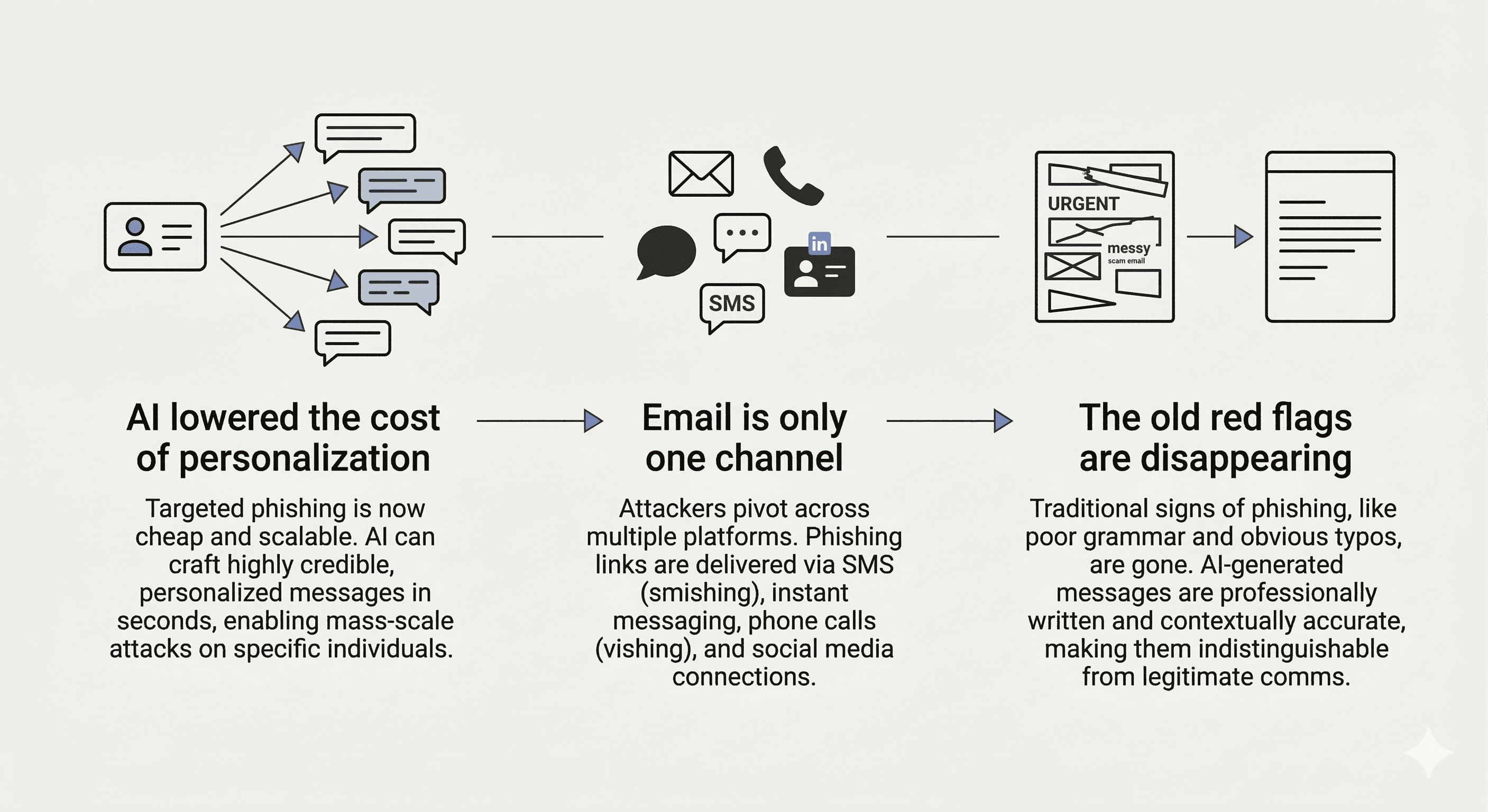
AI collapsed the cost of running a sophisticated, targeted attack.
Researching a target, building a convincing persona, crafting a message that felt personal -- that used to take a lot of effort, which meant it was reserved for high-value targets like executives, politicians, and critical infrastructure. Everyone else got the spray-and-pray version.
Now it takes minutes and can be done at scale against anyone.
Email is just one channel.
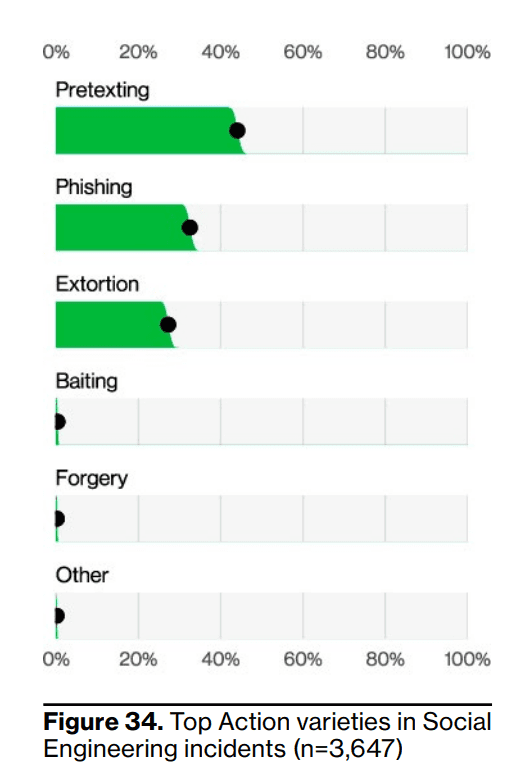
According to the 2024 Verizon DBIR, more than 40% of social engineering incidents involved pretexting, and 31% involved phishing.
Email still matters. The problem is that security training often treats email phishing as the whole category.
A training program that only tests email is measuring one part of the problem.
Some vendors have responded to this by adding attack vectors like SMS simulations, voice phishing tests, and Teams messages.

But that's a race nobody will win.
The moment you add SMS simulations, attackers are somewhere else. You can't simulate your way across an attack surface that changes faster than you can build templates.
The tells we trained employees to spot are disappearing.
Bad grammar, unknown senders, suspicious links - these existed because attackers were running volume operations and didn't have time to be careful.
AI-generated messages are clean and contextually aware. The red flags your program taught people to look for are being engineered out.
What training is actually supposed to do
Most programs are designed to reduce click rates on simulated phishing emails. That's the metric, that's what gets reported upward.
But click rates don't tell you whether your finance team would pause before wiring money based on an urgent Slack message from someone claiming to be the CFO. They don't tell you anything about what happens when an attacker calls your IT help desk.
The distinction that’s important is the difference between teaching people to recognize specific red flags versus teaching them to recognize how manipulation works.
Take the MGM employee. There was no obvious reason for that person to be suspicious: the caller knew names, titles, and context. In that moment, the employee did what people are usually trained to do in every other situation. They tried to be helpful. Training someone to spot a phishing link gives them very little when the attack arrives as a friendly phone call.
If your employees understand that attackers manufacture urgency to short-circuit careful thinking - that this is the pattern, regardless of whether it arrives by email, phone, or WhatsApp - that understanding is multi-dimensional. It doesn't falter when the attack format changes.
Phishing training works to make click rates go down.
The problem is that click rates were never a measure of the whole problem. They were a measure of how well your employees learned to play the simulation. Those are different things, and for a long time nobody in this industry wanted to say so out loud.
Why we built Anagram the way we did
Security awareness training is one of the few enterprise products that every single employee in a company has to use.
….which means it has more in common with Duolingo or TikTok than it does with your SIEM.
Those companies figured out something that the security training industry never bothered to: attention is the hardest thing to get, and if you don't respect it, people will find ways around you.
Hit mute, move the video to a second monitor, click through the quiz. We've all done it.

So we took zero inspiration from existing security awareness vendors and a lot of inspiration from how consumer products actually hold people's attention.
Modules under 60 seconds. Role-specific, so a developer isn't sitting through the same content as someone in finance. Built around how social engineering works, not what a phishing email looked like in 2015.
The goal is employees who understand the manipulation, not employees who can pass a simulation. Those are different things, and only one of them prepares you for a phone call.
If you want to see how we do it differently, book a free demo.
© 2026 Enigma Analytics, Inc.
All rights reserved.




